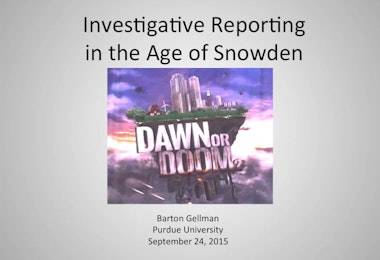
Barton Gellman is an author, journalist and former senior fellow at the Century Foundation. In 2013, Gellman led The Washington Post’s Pulitzer Prize-winning coverage of U.S. government surveillance after receiving an archive of NSA documents from Edward Snowden. His professional distinctions include two previous Pulitzer Prizes (individual and team), two George Polk Awards and Harvard’s Goldsmith Prize for investigative reporting. Gellman’s bestselling book, Angler: The Cheney Vice Presidency, won the Los Angeles Times Book Prize and was a New York Times Best Book of 2008. His previous books include Contending with Kennan: Toward a Philosophy of American Power and a history of Princeton’s Woodrow Wilson School of Public and International Affairs.
After twenty-one years at the Washington Post, where he served tours as legal, military, diplomatic, and foreign correspondent, Gellman joined Time magazine in 2010 as contributing editor at large. Since 2011, he has also been a lecturer and author in residence at Princeton and a fellow at New York University’s Brennan Center for Justice. Gellman graduated summa cum laude from Princeton and earned a master’s degree in politics at University College, Oxford, as a Rhodes Scholar.
Bart Gellman Articles & Interviews on NSA/Snowden
Gellman’s first story regarding extensive NSA surveillance: according to top-secret documents obtained by the reporters, the National Security Agency and the FBI are tapping directly into the central servers of nine leading U.S. Internet companies (including Google, Facebook, and Microsoft), extracting audio and video chats, photographs, e-mails, documents, and connection logs that enable analysts to track foreign targets.
- U.S., British intelligence mining data from nine U.S. Internet companies in broad secret program
- Washington Post,
- June 6, 2013
- By Barton Gellman and Laura Poitras
Gellman reveals Edward Snowden as his source as well as Snowden’s reasons for coming forward with information.
- Code name ‘Verax’: Snowden, in exchanges with Post reporter, made clear he knew risks
- Washington Post,
- June 9, 2013
- By Barton Gellman and Laura Poitras
Article describes Bush-era surveillance programs, NSA’s contemporary U.S. operations, and the scope of the surveillance.
- U.S. surveillance architecture includes collection of revealing Internet, phone metadata
- Washington Post,
- June 15, 2013
- By Barton Gellman
The disclosure of classified information reveals the role of a special court in enabling the government’s secret surveillance programs. Judges associated with the court express frustration with the report and the conclusions it drew regarding court’s cooperation.
- Secret-court judges upset at portrayal of ‘collaboration’ with government
- Washington Post,
- June 29,2013
- By Carol D. Leonnig, Ellen Nakashima and Barton Gellman
According to an intelligence budget obtained by The Washington Post, the NSA is paying hundreds of millions of dollars a year to U.S. companies for clandestine access to their communications networks. Mulit-million dollar payments are made for programs capable of peering into the lives of almost anyone who uses a phone, computer or other device connected to the Internet.
- NSA paying U.S. companies for access to communications networks
- Washington Post,
- August 29, 2013
- By Craig Timberg and Barton Gellman
Article reveals the 2013 $52.6 billion “black budget” which was provided to the The Washington Post by Edward Snowden. The budget details the objectives and operational expenses of the 16 spy agencies that comprise the U.S. intelligence community.
- U.S. spy network’s successes, failures and objectives detailed in ‘black budget’ summary
- Washington Post,
- August 29, 2013
- By Barton Gellman and Greg Miller
The NSA tracked calls from a mobile phone enabling the CIA to find the geographic location of the phone and link it to the compound in Pakistan where bin Laden was hiding. The disclosures about the hunt are detailed in U.S. intelligence agencies’ 2013 “black budget” provided to The Washington Post by Edward Snowden.
- To hunt Osama bin Laden, satellites watched over Abbottabad, Pakistan, and Navy SEALs
- Washington Post,
- August 29, 2013
- By Craig Whitlock and Barton Gellman
U.S. computer specialists place foreign networks under surreptitious U.S. control. Documents provided by Edward Snowden and interviews with former U.S. officials describe a campaign of computer intrusion that is far broader and more aggressive than previously understood.
- U.S. spy agencies mounted 231 offensive cyber-operations in 2011, documents show
- Washington Post,
- August 30, 2013
- By Barton Gellman and Ellen Nakashima
The CIA found that a small number of individuals seeking jobs in the intelligence community had “significant terrorist and/or hostile intelligence connections.” The U.S. Government investigates thousands of employees a year to reduce insider threat.
- U.S. intelligence agencies spend millions to hunt for insider threats, document shows
- Washington Post,
- September 1, 2013
- By Carol D. Leonnig, Julie Tate and Barton Gellman
The “black budget” reveals details of the U.S. intelligence community’s focus on Pakistan as a national security concern. Pakistan’s nuclear program seen as a critical threat.
- Top-secret U.S. intelligence files show new levels of distrust of Pakistan
- Washington Post,
- September 2, 2013
- By Greg Miller, Craig Whitlock and Barton Gellman
According to documents provided to The Washington Post by Edward Snowden, Al-Qaeda is exploring ways to shoot down, jam or remotely hijack U.S. drones. U.S. intelligence officials have closely tracked the group’s efforts to develop a counter-drone strategy.
- U.S. Documents detail al-Qaeda’s efforts to fight back against drones
- Washington Post,
- September 3, 2013
- By Craig Whitlock and Barton Gellman
Article describes the NSA’s successful attacks against users of Tor, a free software that allows users to anonymously use the Internet. The documents illustrate the power of the NSA to at least partially penetrate what have long been considered the most secure corners of the Internet. Through Tor, the NSA successfully identified an al-Qaeda operative.
- Secret NSA documents show campaign against Tor encrypted network
- Washington Post,
- October 1, 2013
- By Barton Gellman, Craig Timberg and Steven Rich
The NSA is collecting millions of contact lists from personal e-mail and instant messaging accounts around the world, many of them belonging to Americans. Analysis of that data enables the agency to search for hidden connections and to map relationships among foreign intelligence targets.
- NSA collects millions of e-mail address books globally
- Washington Post,
- October 14, 2013
- By Barton Gellman and Ashkan Soltani
Documents provided by Edward Snowden show that the NSA had extensive involvement in the targeted killing program that has served as a centerpiece of President Obama’s counterterrorism strategy. Documents highlight the death of one bin Laden associate in particular and how the NSA used email to trace and eventually kill him.
- Documents reveal NSA’s extensive involvement in targeted killing program
- Washington Post,
- October 16, 2013
- By Greg Miller, Julie Tate and Barton Gellman
The National Security Agency has secretly broken into the main communications links that connect Yahoo and Google data centers around the world. The NSA sends millions of records every day from Yahoo and Google internal networks to NSA’s own data warehouses, including records of Americans.
- NSA infiltrates links to Yahoo, Google data centers worldwide, Snowden documents say
- Washington Post,
- October 30, 2013
- By Barton Gellman and Ashkan Soltani
Reporters offer additional background, with new evidence from the source documents and interviews with confidential sources, demonstrating that the NSA accessed data traveling between Google and Yahoo cloud data centers.
- How we know the NSA had access to internal Google and Yahoo cloud data
- Washington Post,
- November 4, 2013
- By Barton Gellman, Ashkan Soltani and Andrea Peterson
The Washington Post reported last Wednesday that the National Security Agency has been tapping into the private links that connect Google and Yahoo data centers around the world. Today we offer additional background, with new evidence from the source documents and interviews with confidential sources, demonstrating that the NSA accessed data traveling between those centers.
- Microsoft, suspecting NSA spying, to ramp up efforts to encrypt its Internet traffic
- Washington Post,
- November 26, 2013
- By Craig Timberg, Barton Gellman and Ashkan Soltani
Microsoft is moving toward a major new effort to encrypt its Internet traffic amid fears that the National Security Agency may have broken into its global communications links, said people familiar with the emerging plans.
Additional interviews and stories about Gellman:
- Reporter Had To Decide If Snowden Leaks Were ‘The Real Thing’
- Fresh Air from WHYY
- September 11, 2013
- Media Weighs Competition, Collaboration In Snowden Coverage
- NPR’s All Things Considered
- September 11, 2013
- 1Thought produced by The Century Foundation
- September 16, 2013
- Interview at St. John’s Church
- September 29, 2013
Piece in Wemple’s reported opinion blog discussing Gellman’s stories for the Post but the omission of stories from Time magazine, despite Gellman’s role as contributing editor at-large for Time magazine.
- Time magazine misses Snowden wave
- Washington Post,
- September 13, 2013
- By Erik Wemple
Talk at the Joan Shorenstein Center, Harvard Kennedy School of Government
- “The Snowden Effect”: Leaks and Consequences at the NSA
- October 15, 2013
- Interview with Melissa Harris-Perry
- msnbc,October 27, 2013
- Interview with Gwen Ifill
- PBS NewsHour, October 31, 2013
Sanford School of Public Policy, Duke University
- Leakers or Whistleblowers? National Security Reporting in the Digital Age
- Barton Gellman and General Michael Hayden debate
- November 11, 2013